Delve into the depths of the enigmatic realm of the digital underworld, where information flows freely and identities remain shrouded in secrecy. At the heart of this clandestine network lies the dark web, accessible only through encrypted pathways. These gateways, known as onion links, provide a route into a vast digital landscape teeming with both light and darkness.
Navigating onion links can be challenging to, but the potential rewards can be significant. Within thiscyber sanctuary, users access a wealth of information, ranging from censored content to activists. However, the dark web is also infested with malicious actors, who exploit its anonymity carry out devious schemes.
- Be wary when navigating the dark web, as it can be a dangerous place.
- Use strong passwords and multi-factor authentication to protect your accounts.
- Be aware of phishing scams and malware threats.
Navigating the Labyrinth: A Guide to Onion Links
Onion links can be a intriguing puzzle, often leading to hidden content on the hidden web. To traverse these labyrinthine paths, it's crucial to comprehend their structure and implement the right tools. First, you'll need a secure software that supports dark web protocols.
- Then, familiarize yourself with how to use onion addresses, which typically end in
- Furthermore, be aware that onion links can shift frequently, so always verify your sources.
- Remember, safety should be your highest value. Use a secure connection to protect your identity and prevent potential risks
Utilizing these tips, you can venture into the world of onion links and reveal its hidden depths.
Hidden in Plain Sight: Unmasking Onion Addresses
The obscurity provided by onion addresses has made them a prevalent tool for malicious activity. However, these layers are not impenetrable. Law enforcement and security agencies are frequently developing new techniques to reveal the true identities behind onion addresses. This battle between anonymity and openness is an ongoing dilemma.
- One method involves examining the traffic flowing through onion systems. By identifying patterns and anomalies, investigators can trace connections back to entities in the physical realm.
- Another strategy focuses on exploiting vulnerabilities within the onion architecture. Researchers are continuously uncovering new holes that can be manipulated to breach anonymity.
Finally, the effectiveness of onion addresses depends on the proficiency of both the operators employing them and those trying to reveal their identities. This cat-and-mouse battle is likely to continue as technology evolves.
Deep Dive into Decentralization: Exploring Onion Link Networks
The emerging world of blockchain technology has sparked a massive interest in decentralization. One fascinating aspect of this movement is the exploration of unique network architectures like onion link networks. These intriguing systems, inspired by the layering principle of onions, offer a robust approach to security and anonymity. By encrypting data across multiple layers, onion link networks make it highly difficult for malicious actors to monitor information.
- This article delves into the architecture of onion link networks, exploring their strengths.
- Furthermore, we'll examine the applications of these networks in various fields, from secure communication to private online interactions.
Get ready for a journey into the fascinating realm of onion link networks and their role in shaping the future of decentralized technology.
Beyond the Surface: Unlocking the Secrets of Onion Sites
Deep within the cyber landscape lies a hidden realm knownas Onion Sites. These enigmatic spaces, shrouded in layers of anonymity, have captivated the curiosity of onionlinks individuals alike. Onion Sites, accessible through specialized browsers called Tor, offer a unique level of privacy and anonymity, allowing users to explore the internet with increased protection from surveillance. But behind this veil of secrecy lies a complex ecosystem, teeming with both for those who dare to venture inside.
The Invisible Web: Connecting Through Onion Links
Delve into the enigmatic depths of the web, a realm beyond the reach of conventional search engines. Here, tucked away behind layers of encryption and anonymity, lies the invisible web, accessible only through specialized tools known as onion routers. These gateways allow users to connect anonymously, fostering a network of individuals seeking secrecy.
Navigating this hidden territory requires an understanding of its unique systems. Onion links, disguised as seemingly innocuous addresses, lead to hidden services.
Each click through these onion links peels away a layer of protection, ultimately revealing the data within.
However, be warned: venturing into the invisible web comes its own set of risks. Malicious actors may hide in this lawless environment, seeking to exploit unsuspecting users.
 Michael C. Maronna Then & Now!
Michael C. Maronna Then & Now!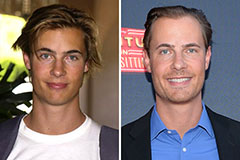 Erik von Detten Then & Now!
Erik von Detten Then & Now! Loni Anderson Then & Now!
Loni Anderson Then & Now! Earvin Johnson III Then & Now!
Earvin Johnson III Then & Now! Ricky Schroder Then & Now!
Ricky Schroder Then & Now!